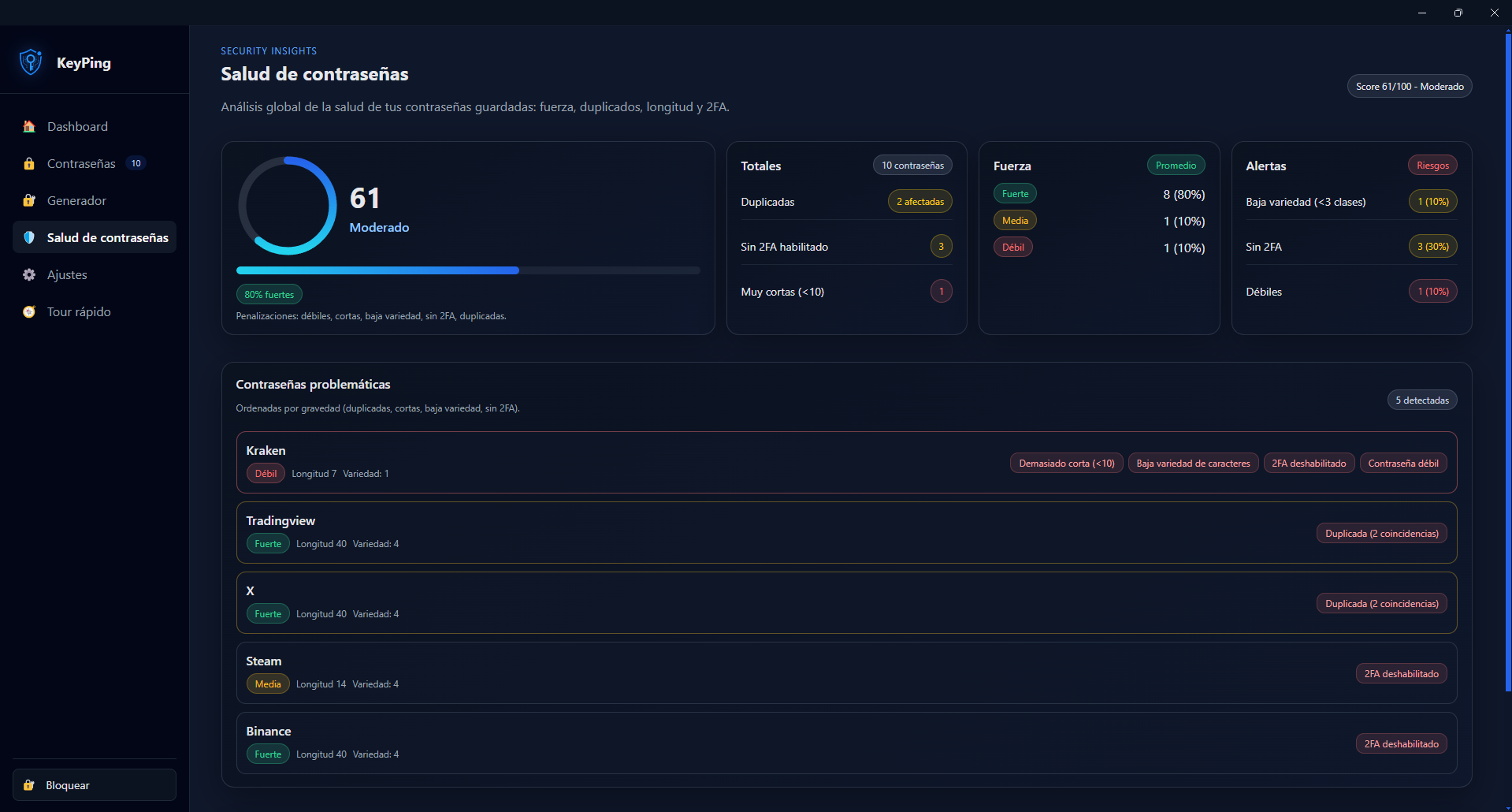
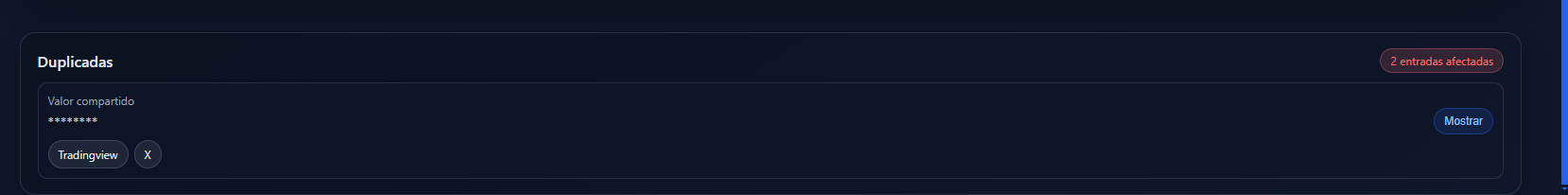
Password reuse
Reused credentials multiply risk across services. One leaked password can compromise several accounts.
FLAGSHIP MODULE // KP-01
Local-first password security system.
Detect weak credentials, enforce hygiene and keep your vault fully offline.
Module Health
Active development / Stable core / Daily use
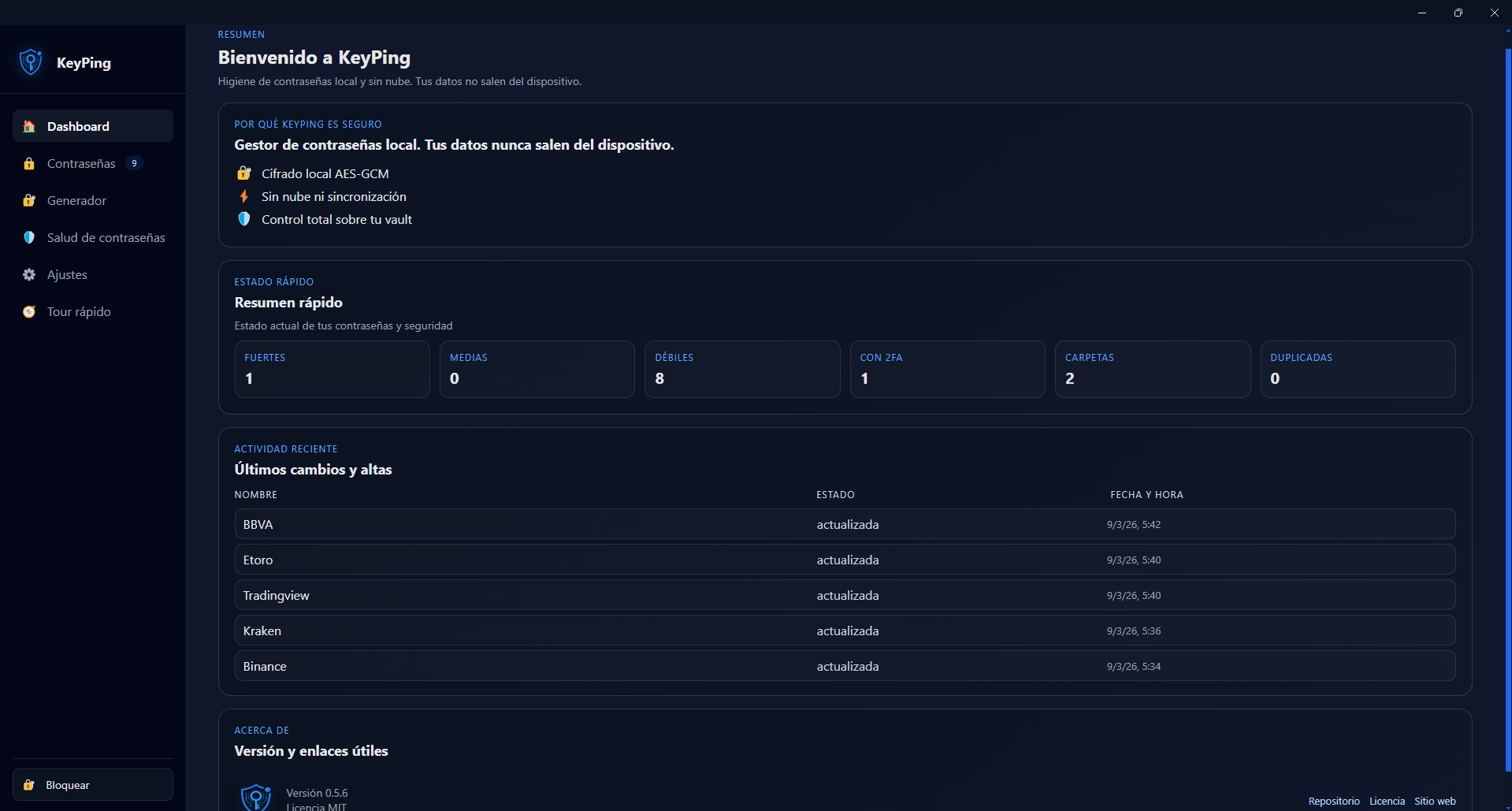
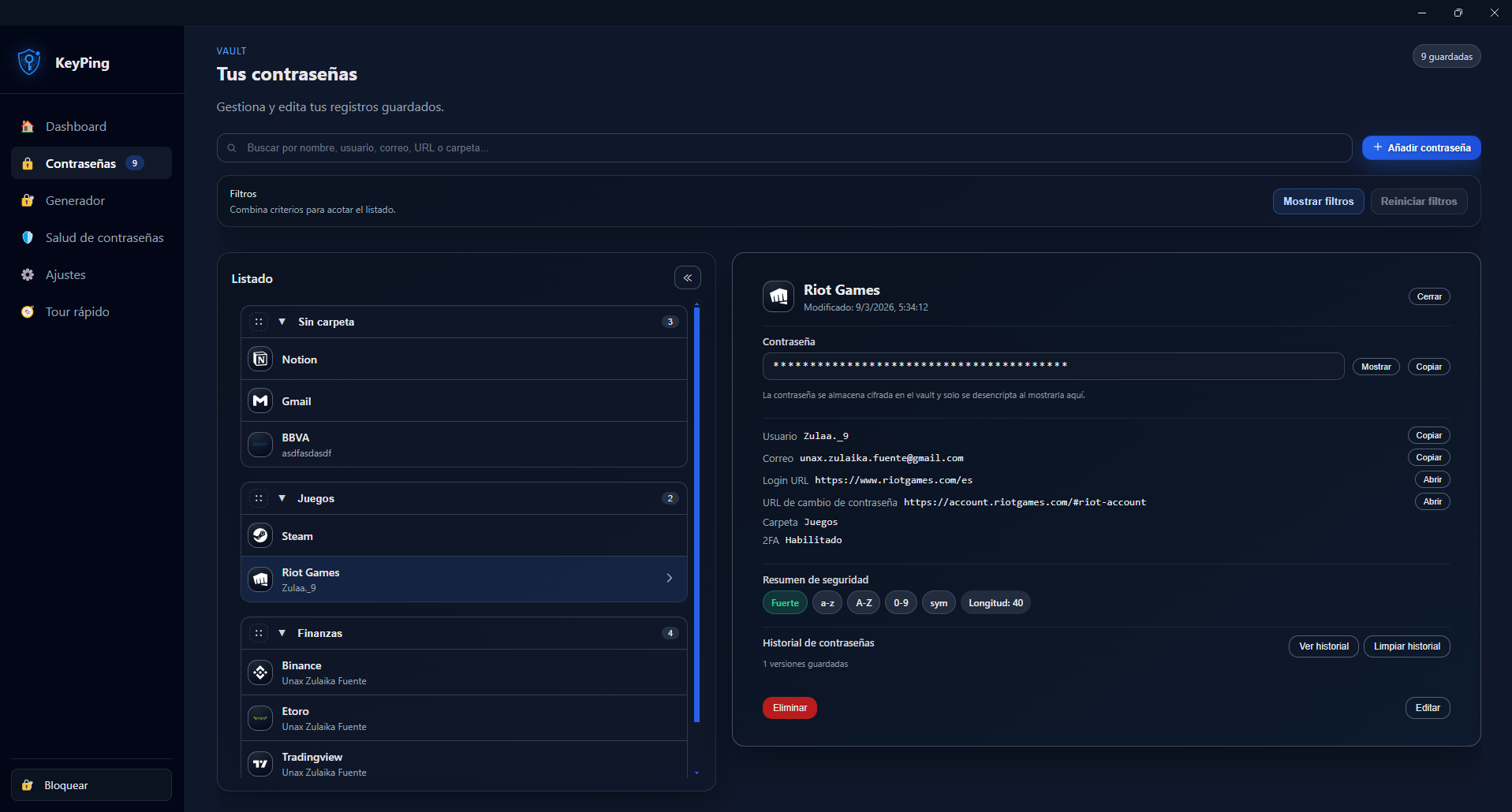
KeyPing is a desktop password manager that focuses on password hygiene: detecting weak, reused and risky credentials while keeping all data local and offline.
This is not a concept demo. It is an actively developed product with stable core features, production-style release discipline, and security controls designed for real usage.
Why this project exists
KeyPing was built to solve real password pain under real pressure, not just to store entries in a vault.
Reused credentials multiply risk across services. One leaked password can compromise several accounts.
Weak patterns are still common. Users need clear signals, not vague warnings, to improve hygiene quickly.
Many managers require cloud trust by default. KeyPing is designed for local-first control.
When incidents happen, privacy and response speed matter at the same time.
Each credential can store a direct password-change URL. In a breach situation, that one-click path reduces friction and reaction time exactly when stress is highest.
Real build signals
Built as a real desktop product with security boundaries between renderer, preload and main process.
Real screens from the app flow: create, generate, inspect and improve password quality.
Frontend Angular standalone components
Runtime Electron
IPC bridge Secure preload API with contextIsolation enabled
Vault Encrypted local file managed by Electron main process
Each release ships with checksums and detached signature files.
Signing key fingerprint
D70937B0AD7411A9E6A66337A5F10A1A37AAEBE9
Verify signature:
gpg --verify SHA256SUMS.txt.asc SHA256SUMS.txtVerify checksums:
sha256sum -c SHA256SUMS.txt